Blog
Top 5 Ways that a GRC Portal Simplifies Third-Party Risk Management
Investing in GRC automation technology often benefits power users, but what about occasional users like leaders, contributors and vendors? A well-designed GRC portal can make a world of difference.
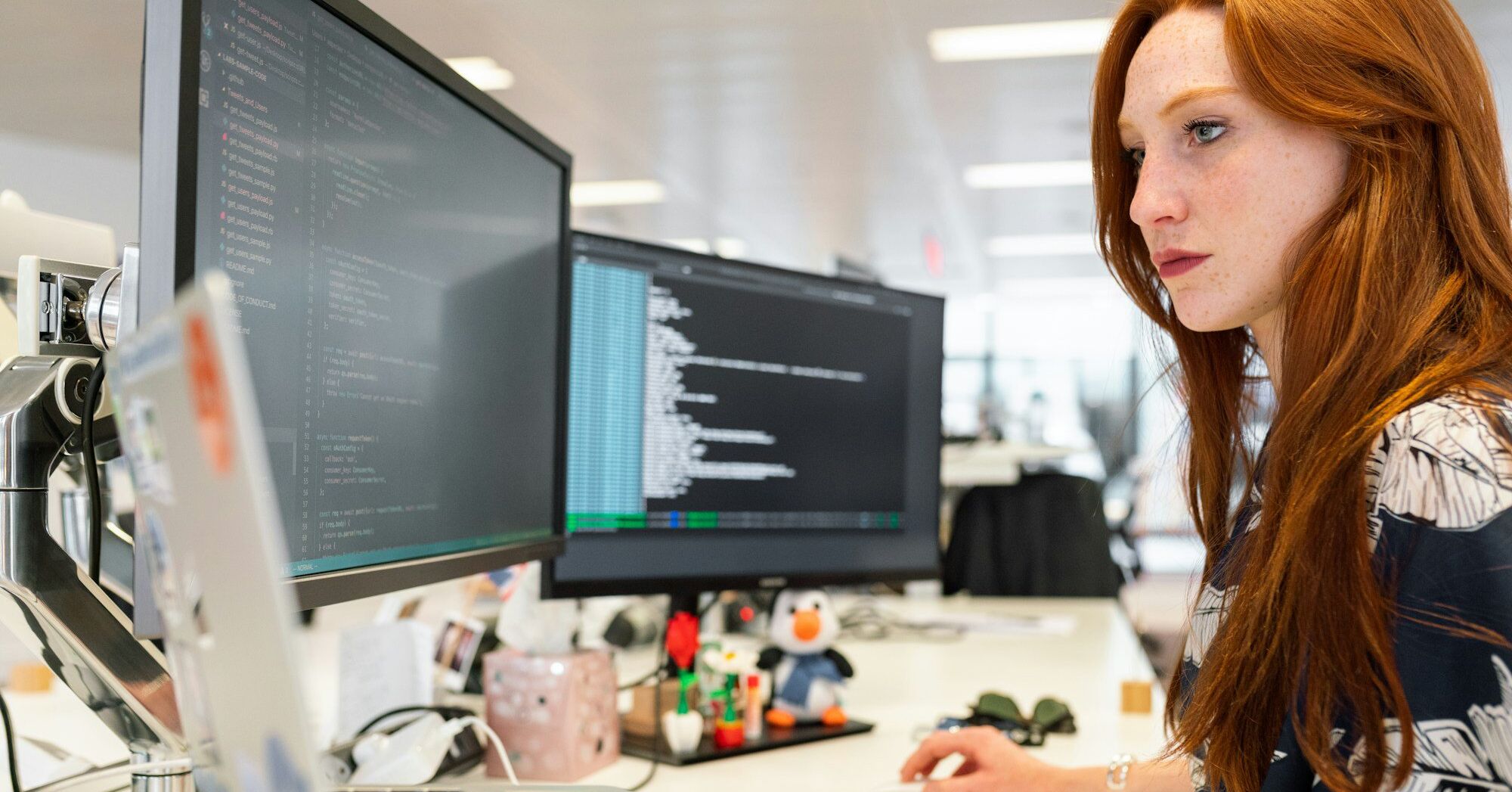
Mental Health in Cybersecurity: Insights from Industry Experts
Explore the link between mental health and cybersecurity in this insightful webinar featuring Cybersecurity Director, Tamika Bass. Discover strategies to manage stress in this high-pressure industry and foster a healthier work environment.
Automating Your Internal Audit Checklist: 7 Tips You Need To Know
Discover how automation elevates the well-designed internal audit checklist into a strategic tool for spotting vulnerabilities, ensuring compliance and delivering big insights.
The Human Firewall: Why Prioritizing Mental Health is Essential for Cybersecurity Success
With such high-stakes in cybersecurity—where constant vigilance and rapid decision-making are non-negotiable—the mental health of professionals often takes a back seat.
What is Remediation in Cybersecurity and Why Does It Matter?
Discover the importance of cybersecurity remediation in protecting your organization from cyber threats. Learn about the remediation process, key statistics, and how to implement effective strategies to enhance your security posture and ensure compliance.
NIST CSF vs. ISO 27001: Choosing the Right Cybersecurity Framework for Your Business
Discover the similarities and differences between NIST CSF vs. ISO 27001 in our comprehensive guide. And find out which framework suits your business best.
How Automation Can Simplify Your Path to NERC Compliance
Digital tools for acheiving NERC compliance can streamline workflows, automate tasks, and deliver real-time insights—making compliance not just achievable, but efficient.
How to Conduct an Information Technology (IT) Risk Assessment
Learn about IT risk assessments, including how to identify vulnerabilities, enhance cybersecurity and develop effective mitigation strategies to protect your IT infrastructure from potential threats.
Top 5 NERC Certification Mistakes and How to Avoid Them
NERC certification mistakes can lead to delays, penalties or operational disruptions. Learn how to avoid these 5 common pitfalls.
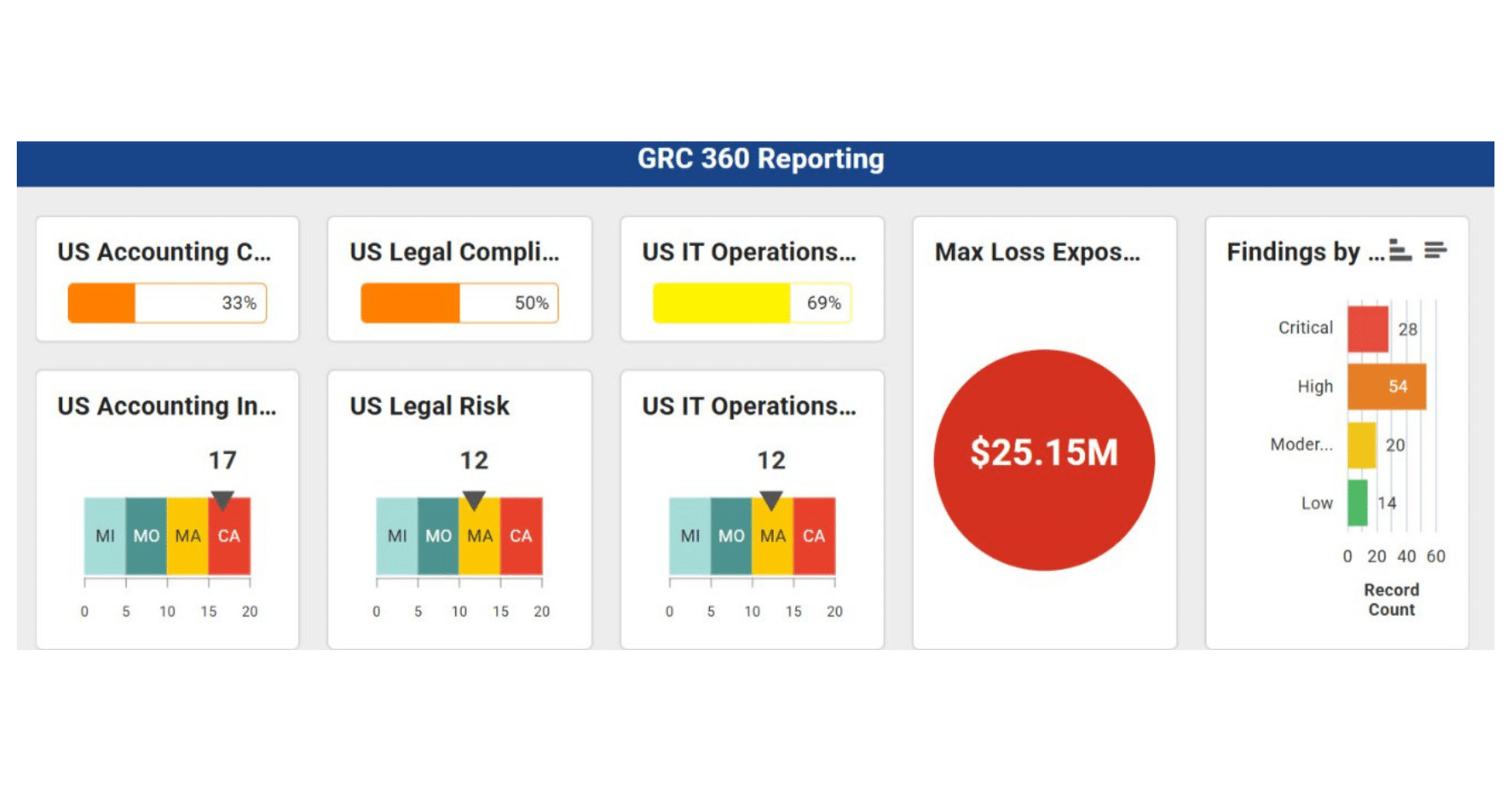
How a GRC Dashboard Can Transform Your Data
Discover how GRC dashboards can offer transparency and actionable intelligence by providing a comprehensive, real-time overview of governance, risk, and compliance activities.