Blog
A Quick GRC Guide to Retail Compliance Management in 2025
With AI, blockchain and evolving regulations reshaping the landscape, retail risk managers across sectors must stay agile and innovative in their compliance management this year. How well are you navigating these challenges?
3 Ways to Expand the Scope of Your GRC Strategy
Learn how organziations strategized and grew their GRC automations to enhance their overall governance, risk, and compliance efforts.
Decoding the Latest HIPAA Security Rule Proposals for 2025
Get our take on updates in the new HIPAA Security Rule proposals aimed at enhancing cybersecurity in healthcare, including mandatory written policies, asset mapping, business resiliency and improved business associate management.
How to Present KRIs Effectively to Your Board: A Coaching Guide
Presenting KRIs effectively to your board can transform risk management from a reactive chore into proactive leadership. This guide offers step-by-step insights on aligning KRIs with business strategies, leveraging technology, and using clear communication to make your data impactful and actionable.
The Department of Health and Human Services Office for Civil Rights (OCR) “Wall of Shame” and Third-Party Involvement
Dive into the HHS OCR’s “wall of shame” to uncover key insights and learn how to better mitigate third-party risks in your organization.
5 Signs Your SLED Agency is Ready for Automated Policy Management
Discover the 5 signs your State, Local or Education agency is ready for automated policy management to streamline compliance and efficiency.
3 Proven Insights for Choosing the Perfect GRC Platform
Get firsthand insights from Jennifer Plowman of TransUnion on selecting the perfect GRC platform. Learn how predictive benchmarking, real-time data and leading indicators can transform your risk management strategy.
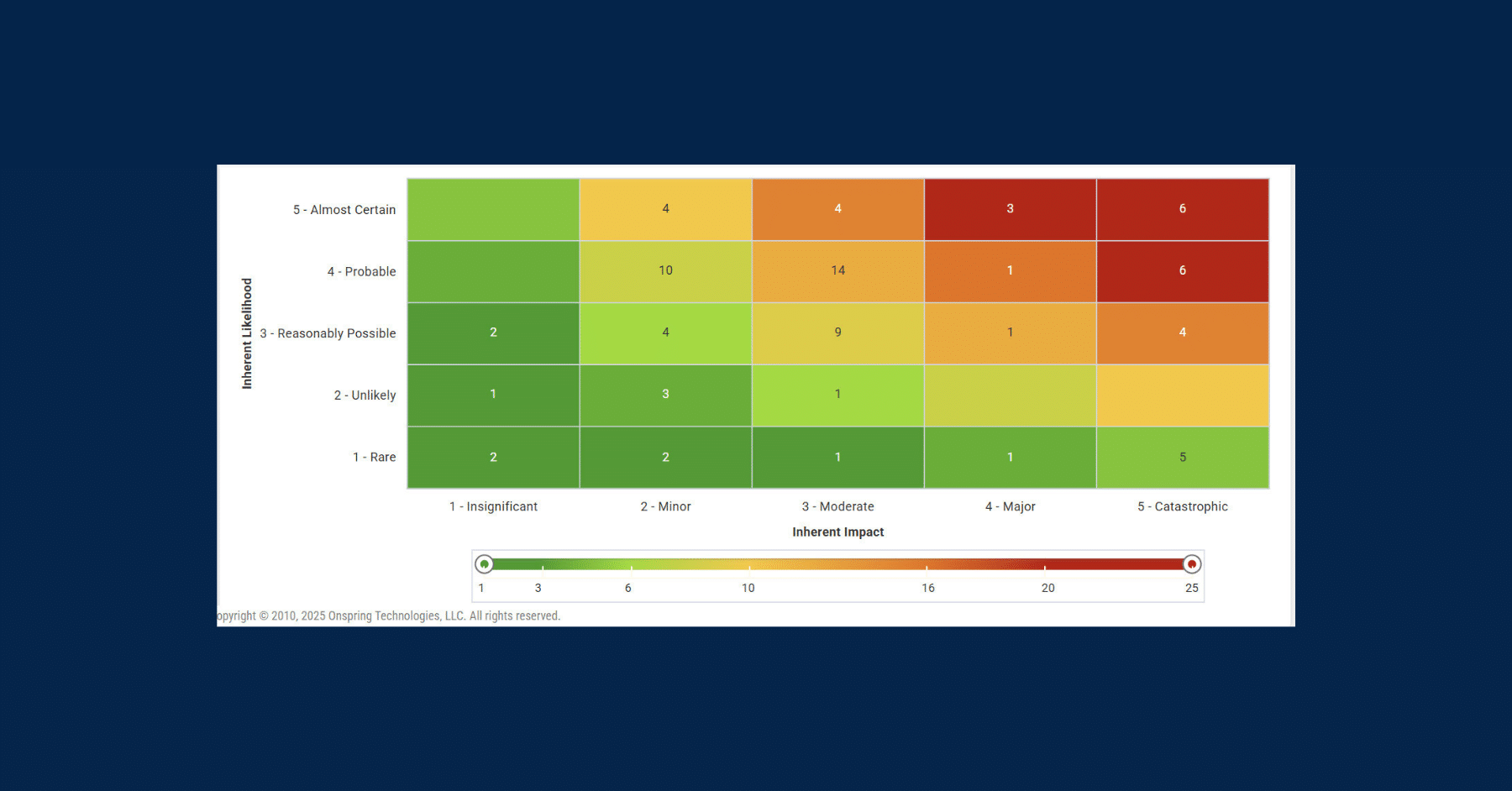
What is a Risk Assessment Matrix?
A risk assessment matrix helps you identify, prioritize, and tackle potential threats efficiently. Learn how this strategic tool can keep your projects on track and compliant ensuring success amidst uncertainties.
3 Best Practices for Vendor Master Data Management
Learn best practices for ensuring data accuracy and establishing robust capture protocols to streamline vendor master data management.
DORA, The Explainer
With stringent requirements for ICT risk management and third-party oversight, the Digital Operational Resilience Act (DORA) ensures that financial entities are fortified against digital threats. Get up to speed on before the next deadline.