Blog
Filter by Product
How to Choose the Right Risk Strategy for Different Types of Risk
Choose the right risk strategy using likelihood and impact to improve risk visibility and align with GRC best practices.
The Next Evolution of Healthcare Cybersecurity: Navigating the Proposed Changes to the HIPAA Security Rule
HIPAA Security Rule updates introduce stricter controls, MFA, and continuous risk analysis—what healthcare leaders must do to prepare.
Gap Analysis vs Risk Assessment: What’s the Difference?
Gap analysis vs risk assessment explained: understand key differences to improve GRC strategy, compliance, and risk prioritization.
Managing Compliance Across Multiple Frameworks in Manufacturing
Manufacturers can simplify multi-framework compliance by mapping controls, reducing duplicate work, and improving audit readiness.
How Real-Time Risk Visibility Supports Smarter Manufacturing Decisions
Real-time risk visibility in manufacturing helps teams reduce disruptions, improve resilience, and make faster, smarter decisions.
Root Cause Analysis: Why It Matters for Risk, Compliance and Incident Management
Root cause analysis helps identify underlying issues to reduce risk, improve compliance, and prevent recurring incidents.
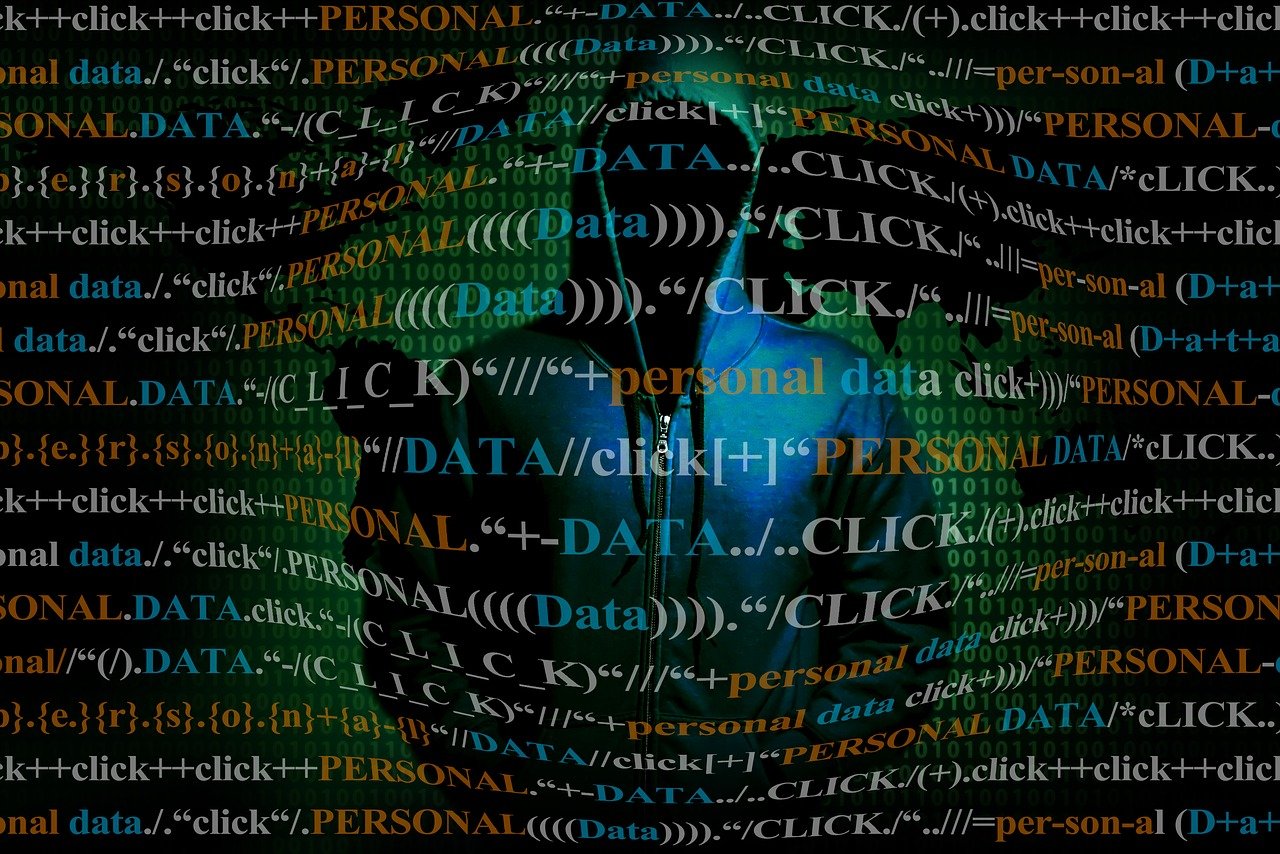
The Hidden Cost of Fragmented Risk Data
Fragmented risk data creates blind spots and delays. Learn how to unify risk data for better visibility and faster decisions.
Measuring Risk Is a Team Sport, Not a Risk Team Responsibility
Measuring risk requires cross-functional collaboration to improve risk visibility, resilience, and strategic decision-making.